Appointment
- Feb 1, 2023
- 2 min read
Enumeration
As usual let's start with our nmap to find out which ports are open on our target machine (Appointment).
nmap -sV IPReplace IP by the IP of the target machine (Appointment)
Note: The IP of our target machine will change all the time, make sure your replace IP in the command below by the target machine's IP. You can find the target's IP directly from your hack the box account.

From your VM, open your browser and type the IP of our target machine (appointment) and press enter:
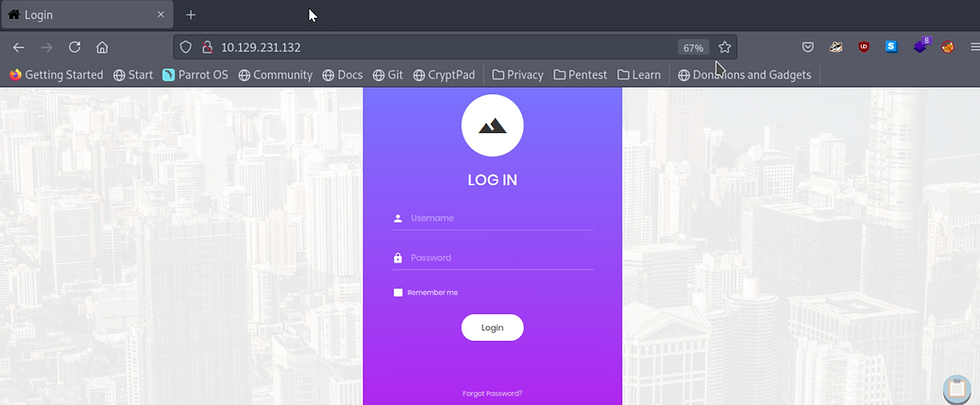
We find a login page but we do not have any credentials available to us to login.
Foothold
Let's first test our luck and try to login with some common credentials like:
username:admin
password:adminusername:guest
password:guestusername:user
password:userusername:root
password:rootusername:administrator
password:passwordNone of these credentials seem to be working.
Now, let's see if the login form potentially has a SQL injection vulnerability!
How does SQL injection work?
When you type your username and your password, both your username and password are passed to the database. The database then checks in its table that you provided the correct credentials before providing you access. It looks like this:
$sql="SELECT * FROM users WHERE username='$username' AND password='$password'";In your login page, let's say you type your username as alice and your password as password123
$sql="SELECT * FROM users WHERE username='$alice' AND password='$password123'";If Alice has provided the correct username and password she will be able to login.
In our case we don't have any credentials available to us. So let's try our SQL injection and see if it works. SQL injection usually works if the programmer forgot to add input validation into their coding. Meaning that we are able to provide a username with characters like ' or #
If we provide our username as admin'# and for the password we type anything, for instance just type the letter p
Then the query will be changed as per below:
$sql="SELECT * FROM users WHERE username='$admin'#' AND password='$p'";BUT we know that everything after # will be recognised as a comment, so the query will look more like:
$sql="SELECT * FROM users WHERE username='$admin'#' AND password='$p'";The comment part will just be ignored and the actual query to the database will be:
$sql="SELECT * FROM users WHERE username='$admin'So this query will just go to the table called users in the database, and look for a username named admin and if it finds a user called admin, it will automatically create a new session without checking that you provided the correct password!
Let's try it on our login page and see if it works!
Let's type:
username ---> admin'#
password ----> p
Click on the login button

We got in!

e3d0796d002a446c0e622226f42e9672
Congratulations you got the flag!
Note: if admin'# didn't work, we could have used administrator'# or root'# for instance. For the password it doesn't matter, we can input anything we like as it won't be taken into account in the sql query.


thanks